Abstract
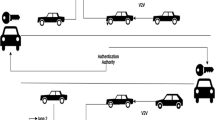
The Internet of Vehicles (IoV) is the Internet of Things where “things” refer to vehicles. Due to its huge amount of shared data and various types of offered services, relying on the use of cloud as infrastructure is fundamental. Most of road services, regardless of whether they are of an infotainment or a safety type, use location and identity information. As a consequence, the privacy of road users is threatened, and therefore preserving such privacy and safety has also become essential. This chapter presents an overview of existing privacy-preserving strategies and develops a proposal for a novel solution which allows its users to benefit from cloud-enabled IoV location-based services and safety applications, anonymously and securely. The performance of the proposed solution is studied by simulating it against a modeled global passive attacker and comparing it to a state-of-the-art solution. The results are optimistic and out-perform the ones compared with. The scheme ensures that the privacy is preserved with more than 70% against semantic, syntactic, observation mapping, and linkage mapping attacks.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Kaiwartya O, Abdullah AH, Cao Y, Altameem A, Prasad M, Lin CT, Liu X (2016) Internet of Vehicles: motivation, layered architecture, network model, challenges, and future aspects. IEEE Access 4:5356–5373
Yang FC, Wang SG, Li JL et al (2014) An overview of Internet of Vehicles. China Commun 11(10):1–15
Mu MP, Khan KUR (2015) Vehicular cloud computing: leading towards tomorrow’s Internet of Vehicles. J Wirel Sens Netw 2(1):1–10
Lucero S (2016) C-V2X offers a cellular alternative to IEEE 802.11p/DSRC. IHS TECHNOLOGY Internet Everything 3:1–3
Hou XS, Li Y, Chen M et al (2016) Vehicular fog computing: a viewpoint of vehicles as the infrastructures. IEEE Trans Veh Technol 65(6):3860–3873
Qin B, Wu QH, Ferrer JD et al (2011) Preserving security and privacy in large scale VANETS. In: 13th International conference on information and communications security, Beijing, China
Pfleeger CP, Pfleeger SL, Margulies J (2015) Security in computing, 5th edn. Prentice Hall, Upper Saddle River, NJ
Benarous L, Kadri B, Bouridane A (2017) A survey on cyber security evolution and threats: biometric authentication solutions. In: Jiang R, Al-maadeed S, Bouridane A, Crookes P, Beghdadi A (eds) Biometric security and privacy. Signal processing for security technologies. Springer, Cham
Singh DR, Yadav RS (2018) A state-of-art approach to misbehaviour detection and revocation in VANET: survey. Int J Ad Hoc Ubiquitous Comput 28(2):77–93
Khodaei M, Papadimitratos P (2018) Efficient, scalable, and resilient vehicle-centric certificate revocation list distribution in VANETs. In: Proceedings of the 11th ACM conference on security & privacy in wireless and mobile networks
Fangchun Y, Shangguang W, Jinglin L, Zhihan L, Qibo S (2014) An overview of Internet of Vehicles. China Commun 11(10):1–15
Gerla M, Lee EK, Pau G, Lee U (2014) Internet of Vehicles: from intelligent grid to autonomous cars and vehicular clouds. Internet of Things (WF-IoT), IEEE World Forum
Kang J, Yu R, Huang X, Jonsson M, Bogucka H, Gjessing S, Zhang Y (2016) Location privacy attacks and defenses in cloud-enabled internet of Vehicles. IEEE Wirel Commun 23(5):52–59
Warren SD, Brandeis LD (1890) The right to privacy. Harvard Law Review, pp 193–220
Lukács A (2016) What is privacy? The history and definition of privacy, University of Szeged
Boualouache A (2016) Security and privacy in vehicular networks. Dissertation, University of sciences and Technology Houari Boumediene (USTHB)
Petit J, Schaub F, Feiri M, Kargl F (2015) Pseudonym schemes in vehicular networks: a survey. IEEE Commun Surv Tutor 17(1):228–255
Boualouache A, Senouci SM, Moussaoui S (2017) A survey on pseudonym changing strategies for vehicular ad-hoc networks. IEEE Communications Surveys & Tutorials
Committee of Intelligent Transportation Systems (2013) IEEE standard for wireless access in vehicular environments–security services for applications and management messages. IEEE Std 1609:2
Sampigethaya K, Li M, Huang L, Poovendran R (2007) AMOEBA: robust location privacy scheme for VANET. IEEE J Sel Areas Commun 25:8
Xingjun S, Huibin X (2014) An effective scheme for location privacy in VANETs. J Netw 9(8):2239
Freudiger J, Raya M, Félegyházi M, Papadimitratos P, Hubaux JP (2007) Mix-zones for location privacy in vehicular networks. In: ACM workshop on wireless networking for intelligent transportation systems
Memon I, Chen L, Arain QA, Memon H, Chen G (2018) Pseudonym changing strategy with multiple mix zones for trajectory privacy protection in road networks. Int J Commun Syst 31:1
Arain QA, Memon I, Deng Z, Memon MH, Mangi FA, Zubedi A (2018) Location monitoring approach: multiple mix-zones with location privacy protection based on traffic flow over road networks. Multimed Tools Appl 77(5):5563–5607
Guo N, Ma L, Gao T (2018) Independent mix zone for location privacy in vehicular networks. IEEE Access 6:16842–16850
Freudiger J, Shokri R, Hubaux JP (2009) On the optimal placement of mix zones. In: International symposium on privacy enhancing technologies symposium. Springer, Berlin, Heidelberg
Lu R, Lin X, Luan TH, Liang X, Shen X (2012) Pseudonym changing at social spots: an effective strategy for location privacy in VANETS. IEEE Trans Veh Technol 61:1
Network simulator 2. https://www.isi.edu/nsnam/ns/. Accessed 22 Sept 2018
Statista (2016) IoT number of connected devices, Statista, November, 2016. https://www.statista.com/statistics/471264/iot-number-of-connected-devices-worldwide/. Accessed 22 Sept 2018
Emara K (2016) Safety-aware location privacy in vehicular ad-hoc networks, Dissertation, University of München
Liao J, Li J (2009) Effectively changing pseudonyms for privacy protection in VANETS. In: 10th IEEE international symposium on pervasive systems, algorithms, and networks (ISPAN)
Boualouache A, Moussaoui S (2017) TAPCS: traffic-aware pseudonym changing strategy for VANETs. Peer-to-Peer Netw Appl 10(4):1008–1020
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Switzerland AG
About this chapter
Cite this chapter
Benarous, L., Kadri, B. (2019). A Novel Privacy Preserving Scheme for Cloud-Enabled Internet of Vehicles Users. In: Mahmood, Z. (eds) Security, Privacy and Trust in the IoT Environment. Springer, Cham. https://doi.org/10.1007/978-3-030-18075-1_11
Download citation
DOI: https://doi.org/10.1007/978-3-030-18075-1_11
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-18074-4
Online ISBN: 978-3-030-18075-1
eBook Packages: Computer ScienceComputer Science (R0)